A forensic examination of the Parity multisig wallet exploit.
Firstly:
Loosing money (or worse getting it stolen) is not a pleasant experience, this article is my attempt to make sense of what happened to round up my understanding of solidity and smart contracts and doing forensic analysis when things go wrong.
Reference:
Coindesk post ( a good overview so far): https://www.coindesk.com/ethereum-dao-fears-forks-finger-pointing-parity-exploit-aftermath/
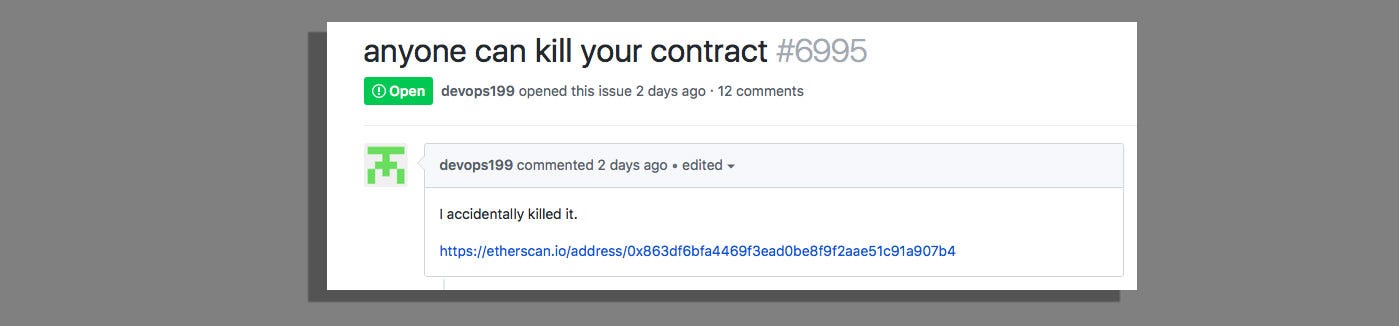
Github Issue: https://github.com/paritytech/parity/issues/6995
Parity Post: https://paritytech.io/blog/security-alert.html
I've tried keeping this discussion accessible, but if you can't make sense of some of it ...I documented my learning curve with smart contracts and turned it into a set of notes here on medium ( and maybe a forthcoming ebook ): Part 1. Setting up.
Part 2. Web3.js/node.
Part 3. Solidity.
Part 4. Smart Contracts.
Part 5. Smarter Contracts.
Part 6. Tokens & Inheritance.
Part 7. ERC20 Token Standard.
Part 8. Crowdfunding and ICOs.
Part 9. Dapps & MetaMask.
Part 10. Remix, Truffle, TestRPC.
Part 11. Some intermediate considerations.
Part 12. Some advanced considerations.
Background:
Parity is a client for the Ethereum Blockchain, it can be used as a wallet or an interface for Ethereum smart contracts. ( see the note on setting up for an overview), this exploit ( as well as a previous one ) only affects multisig wallets in Parity and not regular accounts.
What’s a multisig wallet ?
Good question, let’s make one ( on the Kovan test network ):
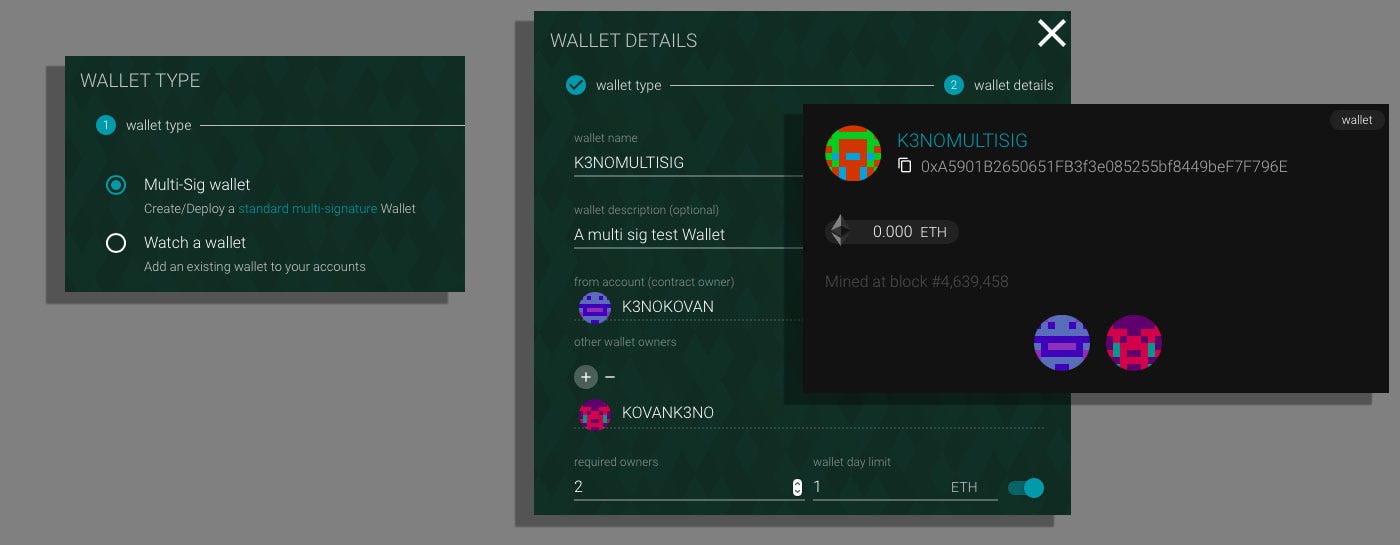
So Parity’s multisig Wallet is a smart contract which provides the functionality of multiple ownership ( owners need to sign transactions ) and wallet day limits. It should be noted that in some sense they are a second class citizens ( a smart contract ) to normal accounts ( first class citizens ), which even before getting into the exploit should raise…
